In a comment, badger points to an IRS memorandum released last Friday: AM2015-005, “International Data Exchange Service (IDES) — responsibility for data transmitted under Sections 6103 and 6105, and tax treaties”. (KPMG has a summary.) Large sections of the fourteen-page memorandum have been redacted, including a page-and-a-half from a three-page section discussing technical details of IDES. (In the technology world, this is known as “security through obscurity”.) Nevertheless, the memorandum still contains some amusing revelations, such as this, from page 1:
We understand that earlier in the development of IDES, oral advice was rendered by Counsel that IDES was a sufficiently secure means of transmission so that using it did not give rise to an improper disclosure of tax return information.
As first pointed out by actual security expert Bruce Schneier in February (and as we discussed last month), in the IDES user manual the IRS recommended the use of the insecure ECB mode of AES in order to encrypt FATCA bank account data uploads. (As of the time of this post, that recommendation still appears on the IDES website.)
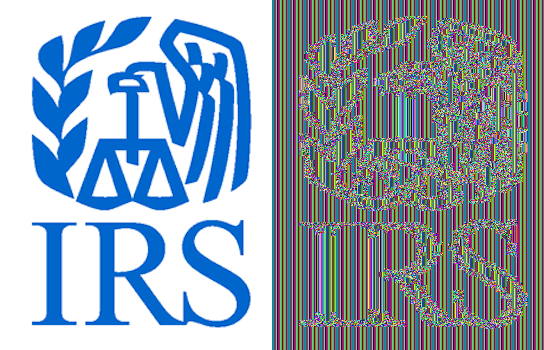
Above you can see the IRS’ logo “encrypted” using these settings. AES, like all encryption, is secure only when used properly; using ECB mode on plaintext which is far longer than the AES block length and has numerous repetitions — like an image with a plain background, or an XML file — does not qualify as proper usage. Apparently someone in the IRS was worried that the suggestion to use these insecure encryption settings could expose the IRS to liability, but rather than asking tech experts to recommend correct settings, they decided it was a better use of IRS employee time & taxpayer dollars to ask lawyers whether it was illegal to recommend incorrect settings.
Even worse, in the latest update to the IDES FAQ, the IRS instructs banks to use totally unsecured-and-unvetted online tools to reformat the FATCA XML files prior to submitting them to IDES. These tools will send the XML file to privately-operated websites with no encryption whatsoever during transit and no guarantee that the owners of the websites will not misuse the data.
No Section 6103 protection prior to IDES upload
The rest of the memorandum includes a lengthy discussion of whether Section 6103 protection arises at the time a non-U.S. bank uploads FATCA data to IDES, or whether protection only begins at the time the IRS downloads the data. (26 USC 6103, “Confidentiality and disclosure of returns and return information”, makes it illegal for U.S. state and federal government employees, and certain other persons with access to return information, to disclose it except in circumstances provided for by that section.) The IRS lawyers weren’t quite sure either way, because ▇▇▇▇▇▇▇▇.
Under the current facts and circumstances, we believe ▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇▇ that 6103 protection arises on the inbound transfer of information at the time that the information is uploaded to IDES. Furthermore, we believe section 6105 and treaty protections are likely to follow the conclusion under section 6103. We understand that the IRS will likely act as if the information were protected at upload and that business decision would be conservative and justified under the current state of the law.
(Note that the IRS staff redacted the PDF file correctly. Apparently they learned something from the woes of the TSA and HSBC five years ago. They didn’t simply change the background colour of the redacted text to black, but completely removed the words underneath from the PDF file. They take the security of Office of Chief Counsel memoranda quite seriously, even if they don’t care about the security of U.S. Persons’ FATCA data.)
However, one thing that’s quite clear from the memorandum, despite the pages and pages of blacked-out sections, is that the IRS lawyers believe there is no Section 6103 protection for FATCA information collected by banks prior to its upload. Conveniently, this position absolves the IRS of all responsibility for illegal disclosure of FATCA data by banks, even though it’s the IRS which demanded that banks act as agents of the United States government to hunt down U.S. Persons and collect all this information on them in the first place.
Recommends insecure online tools to reformat XML
On 14 July, a few days before releasing the above memorandum, the IRS also posted an update to the IDES FAQ. They added questions about currency rounding (A15), enrollment for testing (B9), URL of test environment (B10), confirmation of receipt of uploads (D12), bug causing missing confirmations (D13), who gets a confirmation when a third-party preparer does the upload (F6), IDES enrollment in Model 1 countries (F7), and third-party preparers serving clients in both Model 1 and Model 2 countries (F8).
The answer to D13 is the most disturbing one from a security perspective:
D13. I uploaded a FATCA Report to IDES 3 days ago and have not received a notification about the status of my FATCA Report. Does the XML format cause a problem?
The IRS has identified a specific scenario where notifications are not issued to filers when certain errors are present. A possible cause for a missing notification is XML that is not formatted and is contained on one continuous line. In this scenario, you can reformat the XML into an acceptable format using a variety of online tools, such as XML Pretty Print. The correctly formatted version of the XML can be resubmitted in a new data packet.
So the IRS’ systems are too broken to handle XML without linebreaks, and IRS staff are recommending random online tools to work around the problem. If you go to the website of XML Pretty Print and look at the source code (apparently more due diligence than the IRS did), you’ll find that it does not operate by running Javascript on the user’s machine to reformat the XML, but requires that the XML be sent over the Internet to their servers:
<form method="POST" action="xml-pretty-printer.php">
<p>
A simple <em>XML pretty printer</em>.
</p>
<p>
Put XML in the text area below, click the "<i>Pretty Print XML</i>" button, and see <em>pretty printed XML</em>.
</p>
<textarea name="xml_data" id="xml_data"></textarea>
<input type="submit" value="Pretty Print XML" />
</form>
For those of you to whom that means nothing: when you press the “Submit” button, this will send the data you pasted in the form over the internet to the URL http://www.xmlprettyprint.com/xml-pretty-printer.php. Recall that a FATCA data submission has names, addresses, account numbers & balances, SSNs, and other such private data. If a bank pastes its FATCA data submission into this form for reformatting as instructed by the IRS and then presses “Submit”, the data will be sent to the operators of the XML Pretty Print website.
Worse yet, note the URL: http not https. It’s been well-known ever since online shopping began to become popular in the 2000s that you do not send private financial information like credit card numbers to websites which do not use TLS (those which do will have an https address), because the credit card number will not be encrypted, and every single server through which your credit card number passes in between your computer and the website can see that data.
Note that I’m not blaming XML Pretty Print’s operator for any of this. His website’s lack of support for TLS is not due to some error he made, but because he chose not to pay for a certificate. He probably put up the website to be helpful to folks who need to reformat configuration files and other similar things which don’t need to be kept private and secure. He certainly had no reason to expect a tax agency to recommend that banks use his website to reformat XML files full of private financial data, and would probably be horrified if he found out that they had. Also, I have not the slightest reason to suspect that he is a dishonest person or that he has any intention of saving the data he receives through that form, let alone doing anything untoward with it.
The blame lies squarely at the feet of the IRS. Bank employees should not be sending private financial information in plain text over the Internet to the operators of random websites. Yet the IRS is recommending precisely that. Their technical staff do not even have the level of common sense of the average online shopper.
FATCA data theft will cause security threats in U.S.
Thanks to FATCA, banks with poor security are sending threatening letters to — and gathering up data from — accidental Americans who have no practical connection to the U.S. and have never held its passport. Some of these poor folks are now struggling to apply for Social Security numbers for the first time to comply with the “Internal” Revenue Code. And the vast majority of them will use their newly-minted SSN for nothing else besides writing it at the top of IRS forms; they will not notice if someone steals it and uses it to obtain credit, or social services, or even a U.S. passport under their name.
If Homelanders are very lucky, the identity thieves who steal these accidental Americans’ data from insecure FATCA-ed banks — whether by hacking or by offering bribes to bank employees — will sell the data only to economic migrants who need an SSN in order to work in the U.S., and not to violent extremists who want to attack the country. Homelanders may not care that FATCA threatens the security of U.S. Persons in other countries, but perhaps they’ll care if it threatens their own necks?






@badger
Thank you for your kind words. I posted a short response to PM with a link to this post,
I had misunderstood his initial post; he had referred to (resident) Americans whereas I assumed he was talking about other countries being ready to receive infom FROM IRS. Just in case it matters…??!!
‘Beware of anything with “SMART” attached. It’s usually a 5-letter word for “SPY”.’
That’s why masters of ambiguity call it “INTELLIGENCE”.
I also posted part of this on the FATCA country specific threads, but thought it should go here too:
Egyptian bank outs all those deemed ‘UStaxablepersons’ re FATCA;
http://www.dailynewsegypt.com/2015/09/12/banque-misr-completes-requirement-steps-of-fatca/
“..Banque Misr succeeded in meeting all requirements of the USA Foreign Account Tax Compliance Act (FATCA), before the date announced by the USA Internal Revenue Service (IRS), according to a statement by the bank.
The bank explained that the files of FATCA were sent through the electronic data interchange system, including the number of individual American customers with total balances of over $50,000, or their equivalent in any currency. The files included also the total balances and the number of customers who refused to cooperate with the individuals or the financial organisations which do not have Global Intermediary Identification Number (GIIN).
The bank added that its branches in both the UAE and France also sent the files to the central banks in these countries on time….”
Good to know that now all those USpersons/citizens in Egypt, their assets, and their personal information are now compiled in a handy data package for hackers and terrorists to try and access…..
Does Egypt strike you as a safe place to be outed as a US person/citizen?
See what even the US State Dept says re Safety and Security issues for US citizens in Egypt:
http://travel.state.gov/content/passports/english/country/egypt.html
“..In November 2014, Egyptian terrorist organization Ansar Beyt Al-Maqdis pledged allegiance to the Islamic State in Iraq and the Levant and renamed itself Islamic State – Sinai Province. The group’s association with ISIL increases the risk that terrorist attacks could target U.S. or other western interests, including civilians, and the country’s tourist industry. The group has taken credit for the August 2014 murder of a U.S. citizen in a car-jacking incident in the western desert region. In addition to Islamic State – Sinai Province, there are a number of other terrorist groups operating in Egypt and terrorist attacks can occur anywhere in the country. On June 10, 2015, terrorists attempted to attack the Karnak temple in Luxor, but were successfully engaged by the police before entering the temple complex. On June 29, 2015, Egypt’s Prosecutor General was killed in Cairo when a bomb placed by the side of a road exploded as his motorcade was passing. On July 11, 2015, a car bomb severely damaged the Italian consulate in Cairo.
U.S. citizens should be especially vigilant in tourist areas, practice good personal security measures, and be alert to their surroundings. Travelers should avoid resorts and hotels that lack significant physical setback from roads and adequate security procedures. The Egyptian government maintains a heavy security presence at major tourist sites, especially the resort town of Sharm El-Sheikh and the many temples and archaeological sites located in and around Cairo, Luxor, Aswan and Abu Simbal. U.S. citizens are encouraged to visit the U.S. Embassy Cairo website for the most up-to-date security information…..”……….
………”Restricted Areas: The U.S. Embassy restricts its employees and their family members from traveling outside of Cairo without prior approval and advises all U.S. citizens to carefully consider the security implications of travel outside of the greater Cairo metropolitan area………””
Who could possibly believe that the IRS and US Treasury can really safeguard FATCA data when they can’t even effectively prevent or deal with the identity theft crisis they already mismanage handling regular tax filings – most of which is data that is already present in the US, not being remitted from ‘abroad’?
See;
http://www.procedurallytaxing.com/summer-updates-identity-theft-and-tax-administration-2/
“….the NTA’s June report indicates that the number of open identity theft cases impacting taxpayers in IRS inventory (as of May 2015) swelled again to near May 2013 levels—up 69 percent from May 2014.”
The peak “number of open identity theft cases impacting taxpayers in IRS inventory”: was “……1,901,105 in 2013”
And what does the Commissioner of the IRS say? The very same commissioner of the very same IRS who’ll be receiving and storing and sharing the FATCA extracted data of more than 6-7 million deemed US citizens outside the US, plus the data from who knows how many other deemed ‘UStaxablepersons’ around the globe who aren’t US citizens?
From Koskinen;
“…The Commissioner’s testimony reminded stakeholders that sophisticated cyber criminals present momentous challenges to the Service in an era of archaic IRS technological systems and strained financial resources..”…..
Watcher posted the UK (In)Competent Authority Agreement over on another thread. Some interesting reading, particularly Paragraph 5 (Confidentiality and Data Safeguards).
http://www.irs.gov/pub/irs-utl/United%20Kingdom%20M1A%20CAA%20092315.pdf
I wonder if their recommendation to use XMLPrettyPrint and other insecure websites is in violation of the agreement. Unfortunately as far as I can tell it doesn’t violate 5.2:
Maybe 5.3?
The US’s competent authority is living under asylum in Russia.
@Norman Diamond
Touché.
And just to prove you don’t even have to get fancy to take advantage of FATCA’s obvious security risks, here’s an instant classic phishing tale to warm your heart:
http://fullerllp.com/irs-tax-scam-fake-form-w-8ben/?utm_source=Mondaq&utm_medium=syndication&utm_campaign=View-Original
My employer received that phishing scam by fax, twice. The fax tells the recipient to return the information by fax to a US fax number. Both instances had the same fax number. Someone has to operate that fax number in order to get the phished information. I reported it to the IRS in 2011 and yet the same fax number is in operation in 2015. Now why would the IRS allow it to remain in operation?
There’s more.
http://www.irs.gov/pub/irs-drop/a-00-80.pdf
Page 5:
“Appeals Officer (Customer Service/Outreach) Program
[Office Location]
Toll-Free Number: 1-877-457-5055”
Skype now lets me call US toll free phone numbers toll free, so I tried it. The first time I tried it, the machine rejected my call. But today the machine accepted my call, and the operator tried to sell me something. Now why would the IRS allow that kind of operation?
Another IRS phone number, which I’m too lazy to look up at the moment, was also turned over to scammers. Now why would that be?
Monica Hernandez was not working alone.
@Eric,
Do you see implications from this EU court decision (hat tip to Stephen and the Austrian supporter who passed this on http://isaacbrocksociety.ca/2015/09/20/we-need-69521-by-january-1-2016-to-pay-the-canadian-fatca-lawsuit-legal-bills-and-keep-our-litigation-moving-forward-il-nous-reste-69-521-a-ramasser-pour-notre-poursuite-judiciaire/comment-page-2/#comment-6660929 ) http://uk.businessinsider.com/european-court-of-justice-safe-harbor-ruling-2015-10 for FATCA? It will be interesting to see what EU FIs and Non-fIs do in light of ex. ;
“..Individual European countries can now set their own regulation for US companies’ handling of citizens’ data, vastly complicating the regulatory environment in Europe.
Countries can choose to suspend the transfer of data to the US — forcing companies to host user data exclusively within the country…….” .
from; ‘Europe’s highest court just rejected the ‘safe harbor’ agreement used by American tech companies’ by James Cook and Rob Price.
The article provides a link to the judgement;
http://www.politico.eu/wp-content/uploads/2015/10/schrems-judgment.pdf
The rest of this conversation https://taxlinked.net/taxlinked/live-events/fatca-webinar-transcript is very interesting too, because it touches on many aspects of FATCA and CBT enforcement, but I’m also posting the following excerpt here because of the issue of problems with uploading/transmitting the data:
“……PROFESSOR BYRNES: I can tell you that there’s some model two FFIs and some South American—and I’m not going to name the country, but there’s some South American non-IGA FFIs who want to be compliant and they’re trying to use—okay, I don’t mean there’s two of them off hand, but I know that these two institutions were trying to meet the deadline to translate their data into the XMS sheet that the IRS needs it in from foreign languages, mind you, because they’re not English mother tongue institutions.
So they’re translating it. I think they’d gotten that far although there might have been some, you know, bad data in that conversion but they were trying to upload it to the new IRS IDF system. The, you know, the FATCA input system? And they were unable to do it. They were unable to get the—I’m not a software engineer like Haydon is, but they could—it wasn’t … the upload on the IRS side wasn’t taking the information. I don’t know what you call that in software engineering language, but it wasn’t validating or whatever—Haydon can better explain it, but I know that as a fact was happening at least about a month ago and people were calling me asking about like, “What’s going on?” I’m like I don’t know. Call Haydon.”
HAYDON PERRYMAN: Well, I’ll keep it brief, but there have been some jurisdictions where is has been very tough to register in if you’ve got the very best of intentions to comply. Keeping it very brief right, one of those jurisdictions would be Luxembourg, because the Luxembourg government doesn’t have its own portal that’s free like other jurisdictions. You have to—it’s a paid service. You have to go with Fundsquare or SOFiE. And that takes funds off contract so and so forth.
Another example was South Africa where there was a problem with the data conversions with their instructions. If you followed their instructions to the letter, then you couldn’t submit, it was invalid and it got sent back to you. You didn’t know why. So, Professor Byrnes is right, there have been a lot of jurisdictions that have made it next to but not quite impossible to submit on time, even if you’ve got the very best intentions….”………….
Thanks for posting that, badger. I listened to it live, if I remember correctly, and it was very good. Valuable to have it in transcript form. I look forward to readying it, as a few points really stood out while I was listening to it.
Related in general terms, thought unfortunately they don’t mention IDES or FATCA data theft in general, only E-File PINs: “IRS Fails To Follow Basic Web Security Procedures, Increases Risk Of Taxpayers Identity Theft”
http://taxprof.typepad.com/taxprof_blog/2016/02/irs-fails-to-follow-basic-web-security-procedures-increases-risk-of-taxpayers-idenity-theft-.html
http://thehill.com/policy/finance/269872-tax-foundation-hopes-irs-will-remove-web-feature
Who needs web and PIN hacking? The IRS does it all by themselves. Here’s the latest from https://www.treasury.gov/tigta/oi_highlights.shtml
“Former Internal Revenue Service (IRS) Special Agent Donald Centreal Smith was sentenced in the Northern District of Alabama on November 10, 2015 for his role in a tax refund scheme. Smith entered a guilty plea to conspiracy, wire fraud, and aggravated identity theft in June 2015.
[…]
According to the court documents, Smith began his employment with IRS Criminal Investigation (IRS-CI) as a trainee in 2005 and became a special agent with IRS-CI in 2007.”
This might be interesting:
https://www.treasury.gov/resource-center/sb-programs/SiteAssets/Pages/dcfo-osdbu-mp-forecast/FY%202016%20EXISTING%20Forecast-IRS-FINAL%20as%20of%2010.15.15.xlsx
ex. see Lines 164, 194 and 196
Other FATCA problems and IRS money spent without anticipated results;
“WHAT TIGTA FOUND
The IRS made improvements, based on prior TIGTA reviews, to strengthen systems development requirements management controls for FATCA projects. However, in an attempt to meet the project schedule and manage resources, Withholding and Refund Release 2.0 went forward despite critical data quality problems that resulted in unplanned work and a four-month implementation delay. In addition, improvements are needed to ensure that high-risk issues are given priority.
While the IRS implemented Withholding and Refund Release 2.0 on the revised February 2016 deployment date and there is agreement that the system was built to requirements, the IRS spent $15 million delivering functionality that has not provided the intended business results. The IRS first identified data matching issues in May 2015. Although the initial data matching issues were resolved, the IRS identified new data matching issues as recently as February 2016. The IRS does not have a timetable for when the latest data matching issues will be resolved and automated functionality will provide all of the expected business results.”
https://www.treasury.gov/tigta/auditreports/2016reports/201620077fr.pdf
TREASURY INSPECTOR GENERAL FOR TAX ADMINISTRATION
Office of Audit
Highlights
FOREIGN ACCOUNT TAX COMPLIANCE ACT PROGRAM WITHHOLDING AND REFUND RELEASE 2.0 PROJECT DEVELOPMENT AND TESTING
Final Report issued on August 31, 2016
Highlights of Reference Number: 2016-20-077 to the Internal Revenue Service Chief Information Officer and the Commissioner, Large Business and International Division.
from
https://www.treasury.gov/tigta/oa_auditreports_fy16.shtml
Needs an extra x:
https://www.treasury.gov/resource-center/sb-programs/SiteAssets/Pages/dcfo-osdbu-mp-forecast/FY%202016%20EXISTING%20Forecast-IRS-FINAL%20as%20of%2010.15.15.xlsx
FATCA is mentioned on lines 165, 194, and 196.
$0.00 is budgeted for a contract with Carahsoft which I’ve never heard of.
Millions are budgeted for contracts with Booz Allen Hamilton, which has been in the news recently for two leaks of documents. Nothing to see here folks, business as usual.
“Withholding and Refund Release 2.0 went forward despite critical data quality problems”
How about Withholding and Embezzlement 2.0? Any news on that front? (This question is directed towards TIGTA and US Department of “Justice” not Badger.)
@Norman, thank you for correcting the link.
Admins, could you replace the link I typed at October 30, 2016 at 1:42 am http://isaacbrocksociety.ca/2015/07/22/irs-plays-cya-on-insecure-ides-encryption-for-fatca-data-uploads/comment-page-2/#comment-7700267
and insert this correct one instead?
https://www.treasury.gov/resource-center/sb-programs/SiteAssets/Pages/dcfo-osdbu-mp-forecast/FY%202016%20EXISTING%20Forecast-IRS-FINAL%20as%20of%2010.15.15.xlsx
Fixed the link. Thanks, Badger and Norman.
http://www.accountingtoday.com/news/tax-practice/irs-faulted-for-cybersecurity-weaknesses-79688-1.html
IRS Faulted for Cybersecurity Weaknesses
More criticism from TIGTA of the IRS re data security:
https://www.treasury.gov/tigta/press/press_tigta-2016-37.htm
“Improvements Are Needed to Ensure the Protection of Data the IRS Transfers to External Partners
WASHINGTON — When the Internal Revenue Service (IRS) has shared data, including Personally Identifiable Information, taxpayer information, and other sensitive data, with external entities, it has not always adequately protected the data through secure file transfer technology, according to an audit report that the Treasury Inspector General for Tax Administration (TIGTA) released today.
The IRS shares data with various outside entities including Federal, State, and local agencies; financial institutions; and contractors for tax administration purposes. IRS and Federal guidelines require that sensitive data is protected during transmission to prevent unauthorized access or disclosure. TIGTA initiated this audit to determine whether the IRS is properly protecting this data and whether it is maintaining encryption controls and other security configurations in accordance with the National Institute of Standards and Technology.
The IRS uses three methods to transfer data to external partners: 1) a commercial off-the-shelf product for transfers over the Internet, 2) a commercial off-the-shelf product for direct mainframe-to-mainframe data transfers, and 3) drop boxes to allow the IRS and its external partners to place and retrieve data transfers.
In reviewing all three of these external file transfer methods, TIGTA found the IRS did not ensure that encryption requirements are being enforced and ensure that nonsecure protocols are not being used in order to fully protect information during transmission. These protocols include File Transfer Protocol and Telnet, which are known insecure transfer protocols. The IRS also did not remediate high-risk vulnerabilities or install security patches on file transfer servers in a timely manner. For example, TIGTA found 61 servers with high-risk vulnerabilities, 10 servers with outdated versions of Windows and UNIX operating systems still in operation, and 32 servers missing 18 unique security patches, of which four were deemed as critical. Lastly, the IRS did not ensure that corrective action plans for security control weaknesses met IRS standards. This reduced the assurance that the IRS would correct weaknesses timely.
“It is essential that the IRS fully protect sensitive personal and taxpayer information that it transmits externally,” said J. Russell George, Treasury Inspector General for Tax Administration. “The IRS must ensure that data transmissions are properly authorized and secured, and that remediation plans for correcting weaknesses are effective,” he added.
TIGTA made six recommendations in the report. Of these recommendations, IRS management agreed with two, partially agreed with three, and disagreed with one.
Read the report.
https://www.treasury.gov/tigta/auditreports/2017reports/201720004fr.pdf
Note: The difference between the date TIGTA issues an audit report to the Internal Revenue Service and the date TIGTA publicly releases the report is due to TIGTA’s internal review process to ensure that public release is in compliance with Federal confidentiality laws.”